Trezor Login: Master Secure Access to Your Crypto Wallet
Step-by-step guide for beginners and intermediate crypto users
Why Trezor Login is Critical for Crypto Security
The digital era has made cryptocurrency both accessible and vulnerable. Your wallet’s security begins with the Trezor login. This login combines a physical PIN, optional passphrase, and device confirmation to ensure your funds are safe even if your computer or smartphone is compromised. Unlike software wallets, Trezor ensures private keys never leave the device, protecting against malware, phishing, and unauthorized access.
Think of Trezor login as a layered vault: the PIN is the first lock, the passphrase adds a second hidden layer, and device verification ensures that only you can open the vault. For beginners, this may sound complex, but understanding the process is essential for secure crypto management.
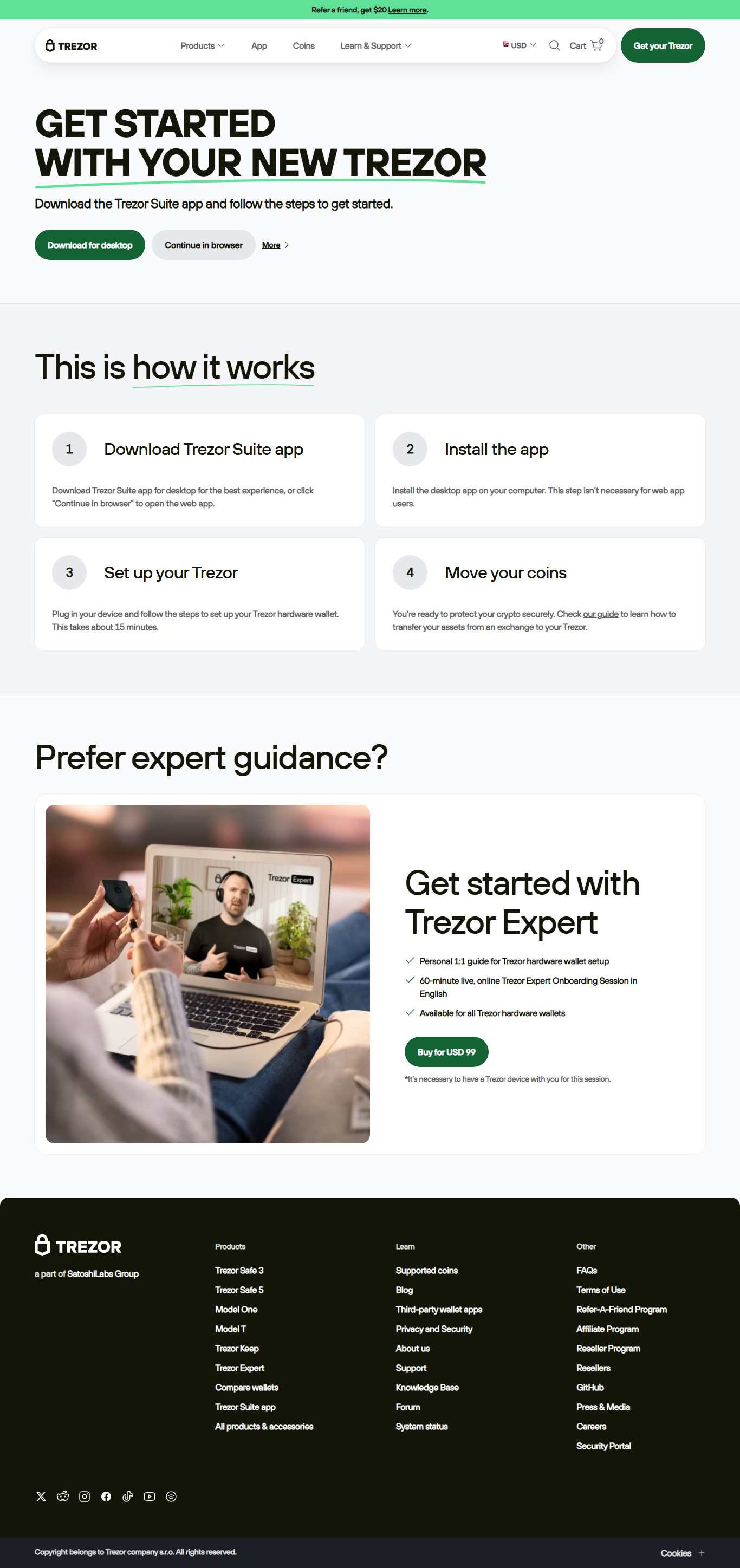
Step-by-Step Guide to Trezor Login
Step 1: Connect Your Trezor Device
Connect your Trezor hardware wallet to your computer or compatible mobile device using the supplied USB cable. Your Trezor screen will illuminate, indicating readiness to login. Avoid connecting to public or unknown computers to minimize security risks.
Step 2: Enter Your PIN
The PIN layout on the Trezor device is randomized. Enter the correct numbers using your computer interface according to the device screen. This randomized grid prevents malware or keyloggers from capturing your credentials.
Step 3: Optional Passphrase for Hidden Wallets
You can add a passphrase to create a hidden wallet. This acts as an extra key; even if someone steals your device, the hidden wallet remains secure without the passphrase. Beginners may skip this, but intermediate users managing high-value crypto should always enable it.
Step 4: Access Trezor Suite
Trezor Suite is the official interface for wallet management. Once logged in, you can view balances, send or receive cryptocurrencies, and authorize transactions. All actions require device confirmation, ensuring no remote access is possible without physical interaction.
Common Trezor Login Issues & Solutions
- Device Not Recognized: Install Trezor Bridge and ensure your firmware is up-to-date.
- Forgot PIN: Use your recovery seed to reset the device and create a new PIN.
- Passphrase Entry Errors: Check capitalization; passphrases are case-sensitive.
- Browser Compatibility: Use Chrome or Firefox, clear cache if needed.
Trezor Login vs Software Wallet Login
| Feature | Trezor Login | Software Wallet |
|---|---|---|
| Security | Offline private keys, PIN + passphrase | Online keys, password only |
| Phishing Protection | Device confirmation prevents fake logins | Vulnerable to phishing attacks |
| Recovery Options | Offline recovery seed | Email or cloud-based recovery |
| Multi-Coin Support | 1000+ coins via Trezor Suite | Varies by app |
Advanced Login Strategies
- Create Hidden Wallets: Protect sensitive assets using passphrase-protected wallets.
- Integrate 2FA: Pair Trezor login with two-factor-enabled exchanges.
- Cold Storage: Keep most crypto offline and only login when necessary.
- Secure Recovery Seed: Store offline in fireproof/waterproof safes; never digitally.
- Limit Login Frequency: Reduces exposure to attacks.
Quick Tips for Safe Trezor Login
Real-Life Example: Protecting Your Crypto
Emma, a crypto investor, attempted to login on a shared computer and received a suspicious browser warning. Thanks to Trezor login requiring device confirmation, her funds remained safe. This demonstrates how the Trezor login’s multi-layer security protects users even in risky environments.
Frequently Asked Questions (FAQs)
Q1: What is Trezor login?
Trezor login is a secure process using PIN, optional passphrase, and device confirmation to access your hardware wallet.
Q2: Can I reset my PIN if I forget it?
Yes. You can reset your device using your recovery seed and set a new PIN.
Q3: Is Trezor login safe on public computers?
No. Public devices may contain malware. Always login on a personal, secure device.
Q4: Do I need Trezor Suite for login?
Yes. Trezor Suite is required to complete the login process and manage your wallet securely.
Q5: Can multiple people use one Trezor device?
While technically possible, sharing is discouraged for security reasons. Use separate devices for multiple users.
Conclusion
The Trezor login is more than just entering a PIN; it’s a sophisticated security system designed to protect your crypto assets. By following the steps outlined, applying the quick tips, and understanding advanced strategies, you can confidently secure your funds. Whether you’re a beginner or intermediate user, this layered approach—combining PIN, passphrase, recovery seed, and physical device confirmation—ensures maximum security in the digital world.